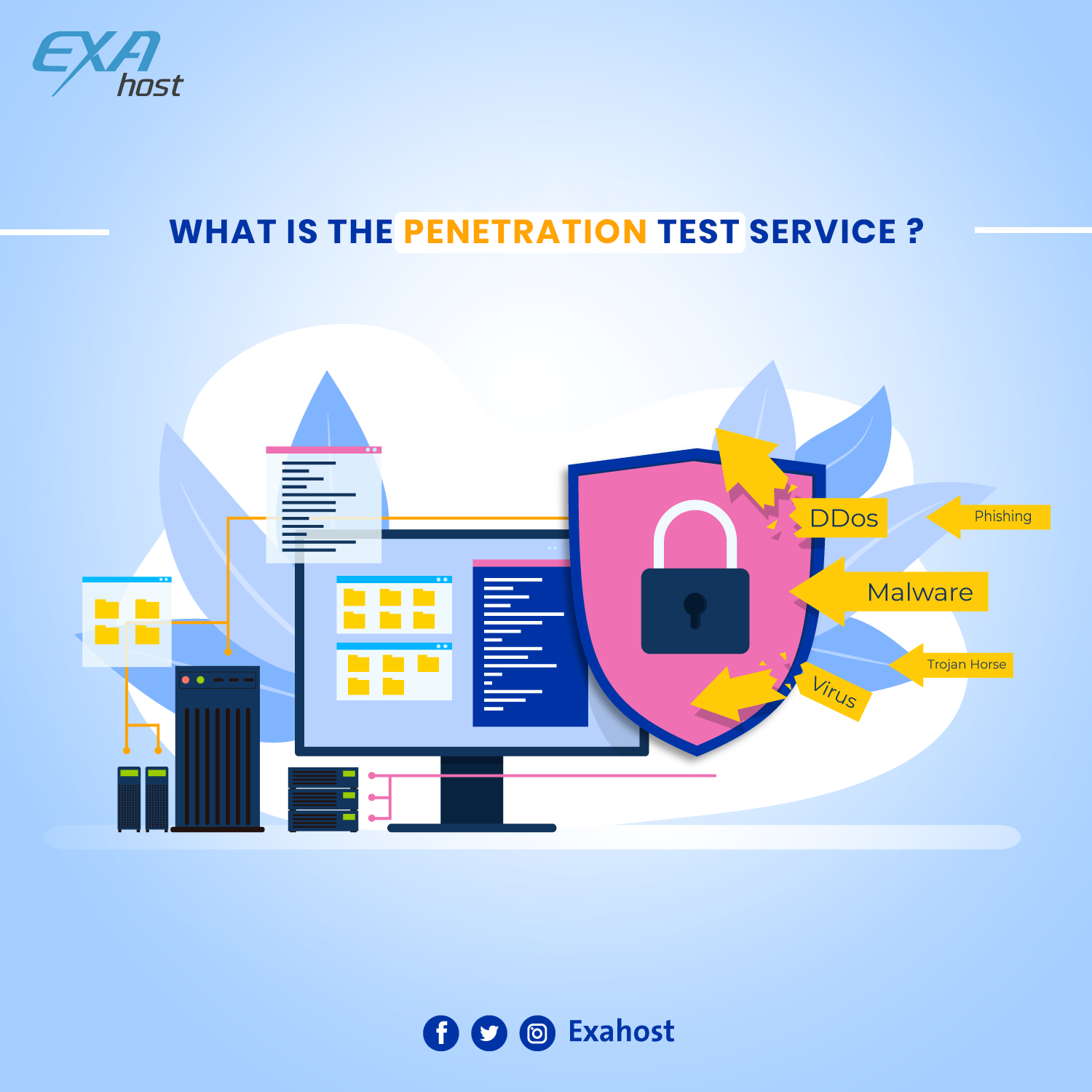
DDOS is an abbreviation for “Denial of Service Attacks” , They are common attacks among hackers, relying on sending requests and commands that exceed the website’s capacity ,by overwhelming the target or its infrastructure with a flood of Internet traffic to prevent the actual visitors from reaching the website .
When these attacks intensively increase , they will badly impact the website’s resources, which will make it almost impossible for real visitors to reach the site, and that can last for minutes or hours and sometimes days .
This kind of attack causes financial losses to large companies that are exposed to them, especially if they do not have strong security strategies to prevent these attacks .
How to protect your website from DDOS attacks ?
Here are some ways to do that
- we recommend using protection scripts, that are available for free or at an affordable price, These scripts will analyze the website’s visits, to tell which are real requests and which are intended to exhaust your server.
- Always buy an additional bandwidth, which is the capacity of transmitting and receiving the data, that will improve the ability to receive and store large amounts of data, giving you more time to respond to the attack.
- You should choose a hosting company that provides internal server security .
- Choose a professional hosting company that knows how to deal with this type of attack, as each company has a security level that should protect your website
- Google has launched a solution to this problem, which is called “project shield” , through which it provides protection for websites exposed to this type of attack , and it may be used by hosting companies .
- Finally, it is important to know that, this type of attack mainly targets businesses that rely on their website, or those dealing with their customers through online stores or online booking .
Here are important facts about DDOS attacks:
- Your website will be badly affected if these attacks took a long time , and may destroy the server’s hardware, because of the excessive consumption of its resources .
- The firewall is not enough to stop this kind of attack, you must contact your network administrator, or technical support to prevent these attacks when they occur.